SPRUIY1D November 2020 – August 2024
- 1
- Description
- Features
- 4
- 1Evaluation Module Overview
-
2Hardware
- 2.1 Board Setup
- 2.2 Hardware Description
- 2.3 Connectors
- 2.4 Mechanical Mounting of the PCB
- 3Additional Information
- 4Revision History
1.3.5 Security
The AM273x EVM can have a Non-Secure (GP or General Purpose) or a Secure device (HS-FS). To determine if the device is secure, refer to field parameter for security: "y" of the Device name. If the Security Parameter is "H", then the device is a Secure device.
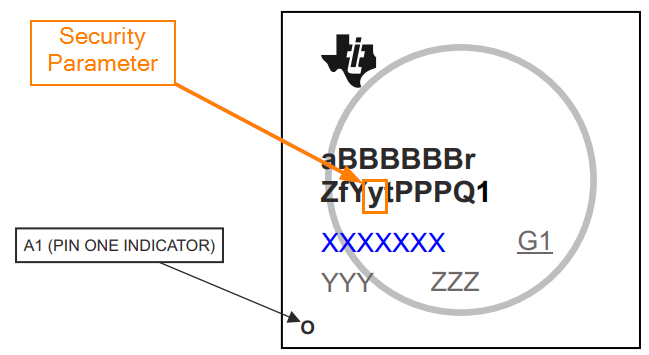 Figure 1-4 Security Field Parameter
Figure 1-4 Security Field ParameterThe AM273x device leaves the TI factory in an HS-FS state where customer keys are not programmed and has the following attributes:
- Does not enforce the secure boot process
- M4 JTAG port is closed
- R5 JTAG port is open
- Security Subsystem firewalls are closed
- SoC Firewalls are open
- ROM Boot expects a TI signed binary (encryption is optional)
- TIFS-MCU binary is signed by the TI private key
The One Time Programmable (OTP) keywriter converts the secure device from HS-FS to HS-SE. The OTP keywriter programs customer keys into the device eFuses to enforce secure boot and establish a root of trust. The secure boot requires an image to be encrypted (optional) and signed using customer keys, which is verified by the SoC. A secure device in the HS-SE state has the following attributes:
- M4, R5 JTAG ports are both closed
- Security Subsystems and SoC Firewalls are both closed
- TIFS-MCU and SBL need to be signed with active customer key